
Web Application Pentesting
What is Web Application Pentesting?
Web Application Penetration Testing, is a cybersecurity practice that involves actively assessing and evaluating the security of a web application. The primary objective of web application pentesting is to identify and address vulnerabilities that could be exploited by malicious actors to compromise the confidentiality, integrity, or availability of the application and its data.
Contact UsWhy Web Application Pentesting is Important?
Web Application Pentesting offers several key benefits for organizations looking to strengthen their cybersecurity posture and protect their digital assets.
Here are some of the prominent advantages:
1. Identifying Vulnerabilities:
Pentesting helps uncover security vulnerabilities in web applications, including common issues like SQL injection, cross-site scripting (XSS), and security misconfigurations.
2. Risk Mitigation:
By identifying and addressing vulnerabilities, organizations can proactively mitigate the risk of security breaches. This helps in preventing unauthorized access, data leaks, and other potential cyber threats.
3. Compliance Assurance:
Many industries and regulatory standards require organizations to conduct regular security assessments, including web application pentesting. Compliance with these standards not only ensures legal adherence.
4. Protecting Sensitive Data:
Web applications often handle sensitive user data. Pentesting helps ensure the confidentiality, integrity, and availability of this data by identifying and addressing vulnerabilities that could lead to data breaches.
5. User Trust and Reputation Management:
A secure web application fosters user trust. Demonstrating a commitment to security through regular pentesting helps build and maintain a positive reputation among users, clients, and partners.
6. Preventing Financial Loss:
Security breaches can result in significant financial losses due to data theft, legal consequences, and damage to an organization's reputation. Pentesting helps prevent such losses by proactively addressing.
7. Business Continuity:
Ensuring the resilience of web applications is crucial for business continuity. Pentesting helps identify potential weaknesses that could disrupt operations.
8. Strategic Decision-Making:
Pentesting results provide valuable insights that can inform strategic decision-making. Organizations can prioritize and allocate resources based on the severity of identified vulnerabilities.
9. Reducing Security Costs:
Identifying and addressing vulnerabilities early in the development lifecycle is generally more cost-effective than dealing with the consequences of a security breach.
10. Continuous Improvement:
Web application pentesting is an ongoing process. Regular assessments allow organizations to adapt to evolving cyber threats, stay ahead of potential attackers, and continuously improve their security posture.
Bulwarkers Approach to Web Application Pentesting:
Unveiling a Strategic Defence Blueprint

1. Information Gathering
Gathering of information through searches of public databases, websites and routing information etc.
2. Scanning
Execution of the scans using automated software tools. Enumeration of hosts, services, application and vulnerabilities.

3. Manual Verification
Verification of the scan results, additional manual discovery and elimination of the false positives.
4. Manual Exploits
Further discovery and exploitation of Manual vulnerabilities using manual Exploits techniques and custom tools an necessary.

5. Analysis and reporting
Analysis of risk and business impact. reporting development of the testing report.

6. Reset and validate
Conduct follow-up testing to verify the effectiveness of remediation efforts and confirm closure of identified vulnerabilities.
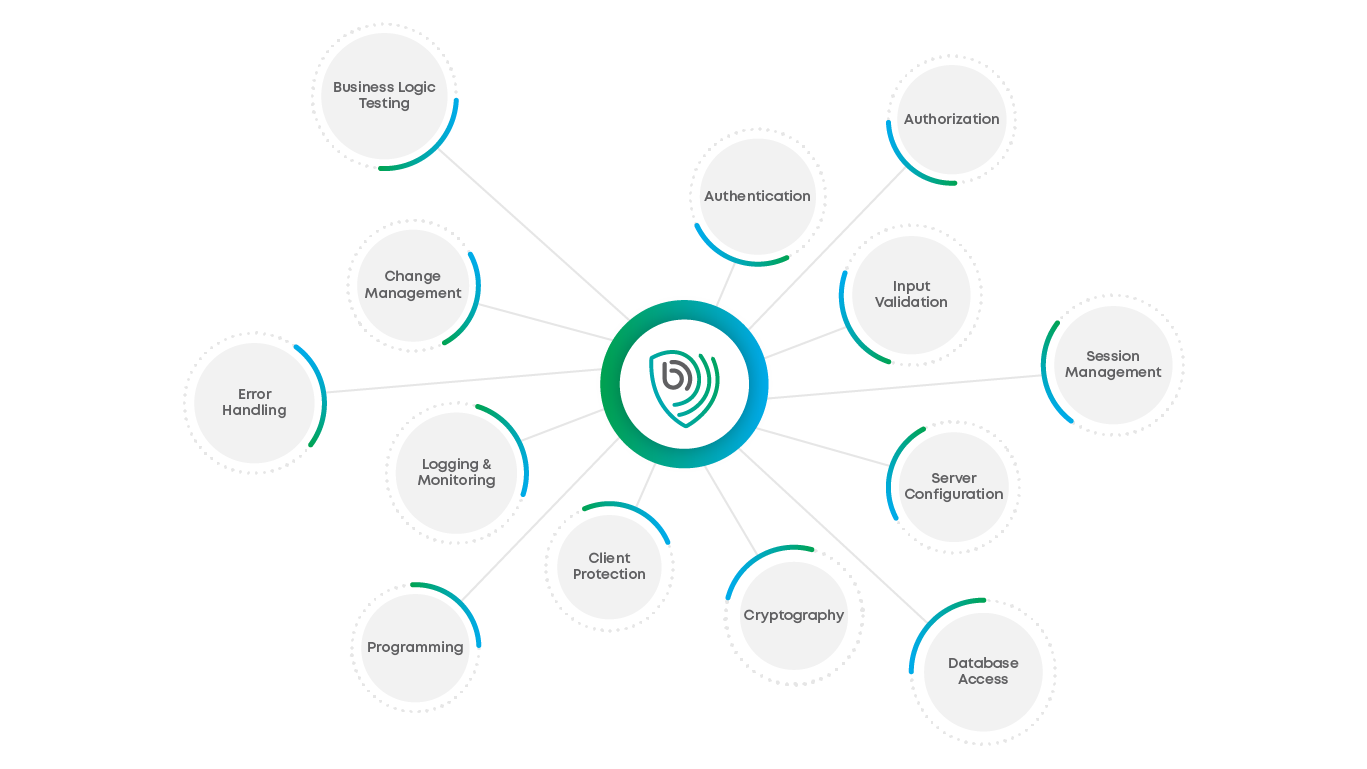
Key Aspects of Web Application Pentesting
CERTIFICATE ACKNOWLEDGED BY THE INDUSTRY
Earn your customers' confidence with a distinct, publicly verifiable certificate of security.
Show off your secure application. Have our engineers check your fixes and secure a unique hosting safety certificate for your product.
Distribute the certificate link to your partners and customers to foster trust-based relationships.

Frequently Asked Questions
VAPT stands for Vulnerability Assessment and Penetration Testing. It is a comprehensive cybersecurity approach that combines the identification of vulnerabilities through assessment with the simulation of real-world attacks.
VAPT is crucial for identifying and addressing security vulnerabilities proactively, reducing the risk of cyberattacks, ensuring compliance, and enhancing overall cybersecurity posture.
Vulnerability Assessment focuses on identifying vulnerabilities in a system using automated tools and manual processes. Penetration Testing, on the other hand, actively simulates cyberattacks to test the system's defences and identify potential points of compromise.
VAPT should be conducted regularly, ideally as part of a continuous security program. The frequency depends on factors such as the rate of system changes, industry regulations, and the organization's risk tolerance.
VAPT is typically conducted by cybersecurity professionals, including ethical hackers and certified penetration testers. These individuals have expertise in assessing and securing IT systems.
Common vulnerabilities addressed in VAPT include SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), insecure configurations, and vulnerabilities outlined in the OWASP testing guide.
Yes, VAPT can be performed on a variety of systems, including web applications, mobile applications, network infrastructure, and other IT assets.
The duration of a VAPT engagement varies depending on the size and complexity of the system being tested. It can range from a few days to several weeks.
A VAPT report includes details of identified vulnerabilities, their severity levels, exploitation paths for successful attacks, and recommendations for remediation.
While fixing vulnerabilities is crucial, it does not guarantee complete security. Regular assessments, continuous monitoring, and a holistic cybersecurity strategy are essential for maintaining a strong security posture.
In many industries, regulatory standards and compliance requirements mandate regular security assessments, making VAPT an essential component of meeting these standards.
Organizations can benefit from VAPT by reducing the risk of security breaches, ensuring compliance, building user trust, and continually improving their overall cybersecurity resilience.